Game Description: In the dark aftermath of the information age, individuals have lost the ability to publicly protect their identities and must take care to safeguard them. Identity is an over-the-shoulder third-person stealth game that emphasizes the importance of guarding and exposing identities. The unnamed protagonist is on a mission to infiltrate Idema Data Network in order to bring down the Cyprium Sever Primus. The player uses their hacking abilities and an identity-stealing ability that allows the player to copy the digital identities of others to fool guards and bypass security.
|
Role: Game Designer
Responsibilities:
|
|
Non-Combative Gameplay
The most distinctive attribute of Identity's gameplay is that the player cannot use violence as a solution against their enemies. The player instead interacts with their enemies and the world by scanning and hacking objects. The eponymous identity-stealing ability allows players to take on the persona of a guard for a limited amount of time and use it to fool guards and security devices. However, guards are not fooled by their own identity so players must pay attention to who is around when they use their stolen identities. Outside of the identity ability, players must avoid and flee from guards before their own identity is stolen and revealed to the world.
In addition to providing a distinct player experience from other popular stealth games, the elimination of combat better fills the player fantasy of a hacker infiltrating a massive corporation. It reinforces the emphasis of cleverness and wits that hackers are traditionally associated with. There is no need to allow the player to pull out a gun and shoot a bunch of enemies in a game that otherwise focuses so much on the future of the internet and the state of information control.
In addition to providing a distinct player experience from other popular stealth games, the elimination of combat better fills the player fantasy of a hacker infiltrating a massive corporation. It reinforces the emphasis of cleverness and wits that hackers are traditionally associated with. There is no need to allow the player to pull out a gun and shoot a bunch of enemies in a game that otherwise focuses so much on the future of the internet and the state of information control.
World Building
User Interface
Identity is a fairly abstract game. Citizens live their lives in fear of losing their personal information and mask themselves. Corporations hold all the information and the tools to blackmail anyone who oppose them. Players do not confront their enemies directly as in most games, nor can they even see the face of any character in the game. Game overs occur when a player is hacked, not when they are detained or killed. Hacking occurs against a player when a guard or a security camera recognizes the player as an intruder and maintains a line of sight. These concepts were not immediately obvious to players, especially early on in development. Therefore it was important to build the world both through writing and visual means. I spent a lot of time with the UI team to develop a user interface that both facilitated gameplay and naturally conveyed to the player that they couldn't nor did they want to use combat in the game. Players were happy to exchange weapons for the ability to scan objects for information and to hack them.
The player scans multiple objects, hacks a guard, steals his identity and uses it to bypass an I.D. door
Introducing The World
From a written standpoint, it was important to set up the world immediately. Both in the opening cutscene and in the interactive tutorial, the player is told who they are and what their main objective is. Stealth is a genre that particularly relies on purpose to drive its gameplay. Aimless stealth quickly loses its appeal since there is no sense of progress. The player is told that they need to take down the Cyprium Server Primus at the top floor of the Idema Data Network and restore free information to the world in the hopes of lifting the desperate measures that the citizenry are taking to avoid losing their personal information, thereby letting other people steal and change it.
Opening Cinematic giving the player quick insight in the setting and purpose of Identity
Developing The World
The opening cinematic only factually states what the player needs to do; there is still much more culture for the player to learn and discover. To give players a better understanding of the world around them, they can hack into several computers to read e-mails of employees at Idema Data Network that explain the context of the world. These require initiative from the player and don't bog the game down for players who are uninterested in the story. The purpose of these e-mails are to describe the loneliness and despair of the dystopia in which society exists in. One of the ways these e-mails communicated the disconnect people have with each other are in the names of the senders and recipients. In the world of Identity, individuals have impersonal names with their job title followed by roman numerals. If players pay close attention, they may bump into a few guards they read about in the e-mails.
The player hacks into a workstation and reads an email between two firewall guards
A.I. Behavior
A.I. Awareness States
There are four major A.I. states involving their awareness of the player: Oblivious, Suspicious, Alarmed and Hacking. Oblivious means the guard is completely unaware of the player's presence. Suspicious means the guard has become aware of the player's presence but does not know he is an intruder. Alarmed means the guard is both aware of the player and that he is an intruder. Hacking means the guard is actively hacking the player to steal his identity.
It was important for the player to be able to escape guards when detected since they have no violent options when guards become alerted to their presence. Because of this, players can outrun guards, crouch and hide behind a variety of objects, crawl in ventilation shafts or briefly break line of sight and activate a stolen Identity to avoid guards. However, to ensure guards were respected by the player, guards can detect the player through sound, vision or nearby security cameras in addition to exclusively using ranged hacking to unveil the player's identity and expose him to the world.
One of the interesting things we learned through testing was that players thought the guards were very smart even when their A.I. wasn't fully developed. The likely reason for this is due to their limited methods of dealing with guards. Because the player doesn't have an easy out when cornered against a wall, I kept the A.I. less intelligent than they could have been to keep the game as forgiving as possible. Ultimately, it matters more if the players think the A.I. is intelligent as opposed to the developers thinking so.
It was important for the player to be able to escape guards when detected since they have no violent options when guards become alerted to their presence. Because of this, players can outrun guards, crouch and hide behind a variety of objects, crawl in ventilation shafts or briefly break line of sight and activate a stolen Identity to avoid guards. However, to ensure guards were respected by the player, guards can detect the player through sound, vision or nearby security cameras in addition to exclusively using ranged hacking to unveil the player's identity and expose him to the world.
One of the interesting things we learned through testing was that players thought the guards were very smart even when their A.I. wasn't fully developed. The likely reason for this is due to their limited methods of dealing with guards. Because the player doesn't have an easy out when cornered against a wall, I kept the A.I. less intelligent than they could have been to keep the game as forgiving as possible. Ultimately, it matters more if the players think the A.I. is intelligent as opposed to the developers thinking so.
A.I. Detection: Sound
Sound detection was important to include for the sake of immersion. Being able to freely run behind guards makes them feel extremely stupid. From a mechanics standpoint, the player generates sound at a distance and intensity based on their movement speed. Guards increase in suspicion when they hear the player's sounds until they finally enter the suspicious A.I. state and investigate the source of the sound. If the player is quietly sneaking near a guard, he might only gain a little suspicion, but if the player runs behinds one, he would immediately become suspicious.
A.I. Detection: Sight
Vision detection was a little trickier. Within a certain conical radius, the player is immediately detected and the guard becomes alarmed and aggressively pursues the player. For longer distances, the guard becomes suspicious while the player in within his line of sight. If the player is not found when the guard investigates, he returns to oblivious. This system gives the guard enough intelligence to force the player to respect him while also giving the player enough time to react to a mistake without it becoming too difficult to recover from.
A guard becomes suspicious of the player at a distance, approaches the location to investigate, detects the player and the hacks him and steals his identity
A.I. Detection: Distraction
Guards also detected noises from certain objects that can be hacked and used as distractions for the player. Once a distraction device has been hacked by the player, the nearest guard will approach the object and spend time turning it off. The player can use this to sneak past them or hack the guard who is distracted. This was a good mechanic to allow players to manipulate the environment and guards to their advantage, giving them small moments of power in a game that otherwise makes them feel vulnerable. I spent a lot of time thinking about a way to empower the player in a manner that fit the game. Combat was out because the player character was not supposed to have any sort of combative training. Direct manipulation of guards also seemed too aggressive and would have made the guards seem more like robots than humans. Therefore this indirect influence through a distraction felt the most appropriate for our game.
The player hacks a distraction to divert a guard and then sneaks by
A.I. Detection: Self-Detection
Guards have the ability to detect a duplicate of their own Identity. This was perhaps the most important way to make guards feel intelligent. It made sense to players that they could steal guard A's Identity to fool guard B, but they found it interesting when guard A's Identity does not work on guard A. This also forced players to interact with more guards as opposed to simply stealing the first Identity that they can find and proceeding to walk in front of that very same guard with it.
The players steals a guard's Identity and attempts to use it to sneak by him but the guard detects a duplicate of his Identity and hacks the player
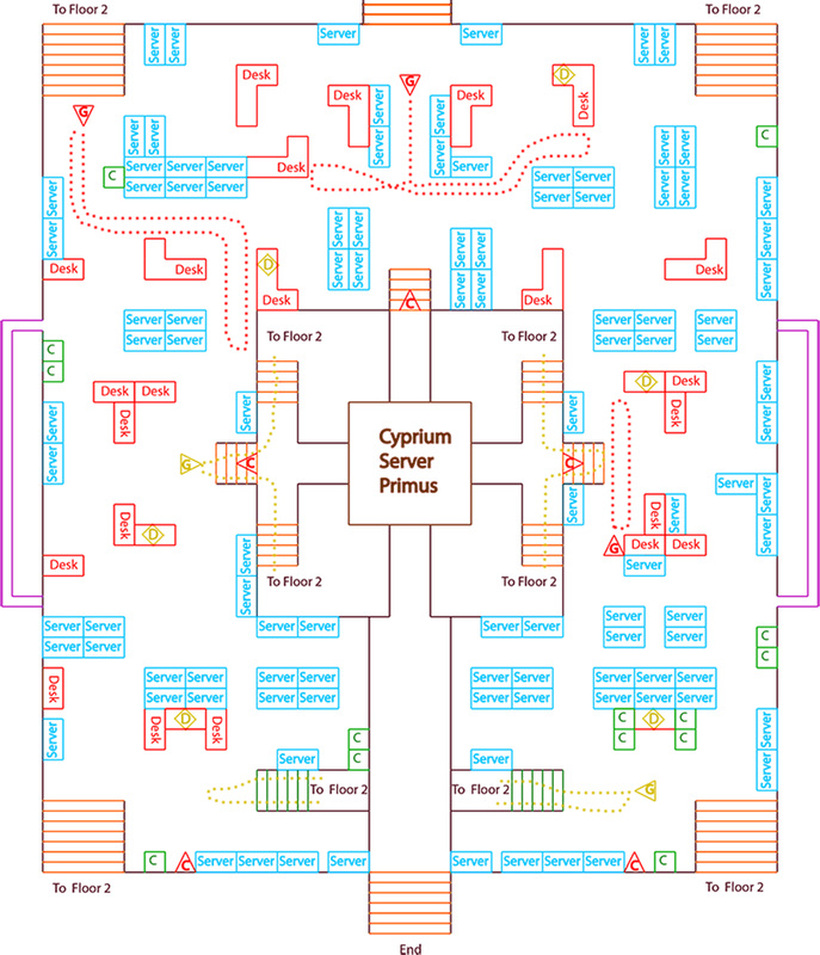
Final Level: Server Room Design
Server Room Design Goals
The major goals for the Server Room were to give the player a chance to utilize all the skills they previously learned in an open and intense scenario. This level takes place in the heavily guarded server room that contains the objective of the game: the Cyprium Server Primus. The Cyprium Server Primus is secured by an exterior shell of servers that must be lifted by four Hackable Terminals before entry is allowed. After each Terminal is hacked, a short cutscene shows the exterior shell rising a bit, giving the player a sense of progress and reminding them of their real purpose. The four Hackable Terminals are in the four corners of the level on the second floor. The player has several tactical decisions to make, both in how to approach any given Terminal and the order in which the Terminals are tackled. Players greatly enjoyed the opportunity to take the initiative when presented with a clear objective and options on how to proceed.
The player methodically goes through the level avoiding guards and hacking the four terminals to gain access to the Cyprium Server Primus
Server Room: Floor 1 Details
The level begins at an elevator on the first floor leading the player directly into the large server room. The first floor focuses around the Cyprium Server Primus and provides paths to the four Hackable Terminals. The area outside of the Cyprium Server Primus is densely populated with server racks that block most long sight lines, allowing players to quickly turn a corner and hide if detected. On the flip side, a guard may be waiting behind every turn, so players must proceed with caution. The environment both enables the player and forces them to respect their foes, creating interesting gameplay. Most of the patrolling guards on the first floor are firewall guards, or guards that are immune to hacking. This means that the player must search for another guard in order to have a stolen identity. Once the player has activated all four Hackable Terminals, the Cyprium Server Primus fully rises and allows entry for the player to hack it and pass through a tunnel to the exit.
The desired player experience on the first floor is haphazard and requires spontaneity from the player since they don't have good information about guard and camera locations at any given moment. The level flow here is rhythmic, bouncing between periods of fast movement and silent pauses.
The desired player experience on the first floor is haphazard and requires spontaneity from the player since they don't have good information about guard and camera locations at any given moment. The level flow here is rhythmic, bouncing between periods of fast movement and silent pauses.
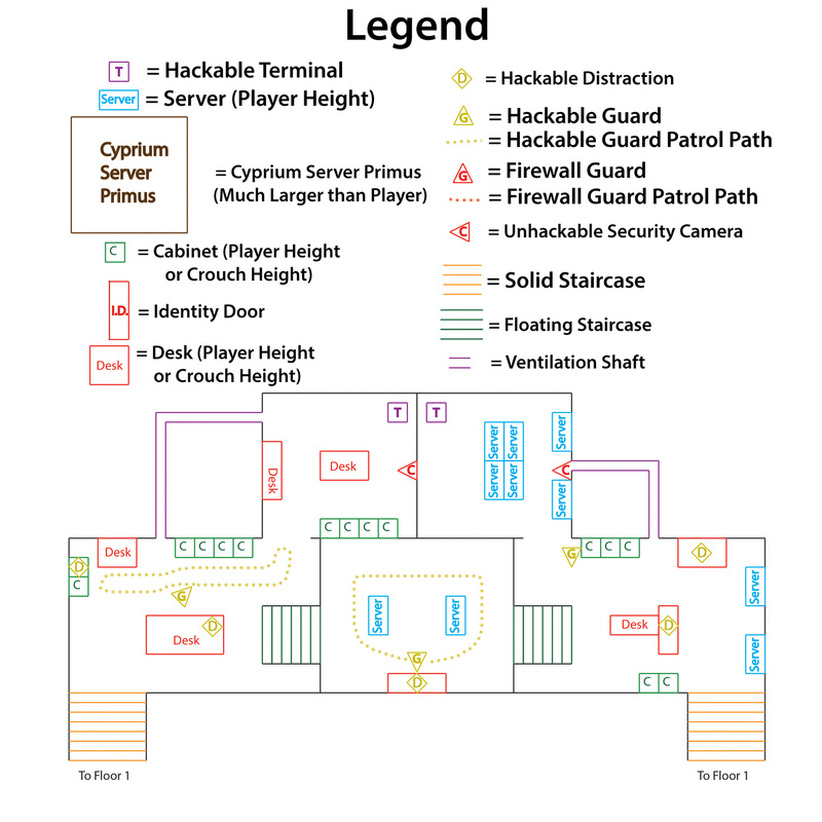
Server Room: Floor 2 Details
Floor 2 is where all four of the Hackable Terminals are located. This floor offers players even more options in getting around enemies. Players may move through alternate vent paths, hide under floating staircases or use stolen identites to bypass security in each of the four sections with the Hackable Terminals. The northern pair of Hackable Terminals are slightly easier to get to because the vents give a clean path to the Terminals that avoid the guards. The southern pair has a vent path that connects the two Terminal rooms to each other, but entering the vents are more dangerous. Additionally, an Identity Door blocks the path on top which means the player must be using a stolen identity to pass through. Also worth noting is the path around the Cyprium Server Primus that allows players to move quickly from one side of the level to the other.
The gameplay on the second floor presents more consolidated and discrete situations to players than the first floor, allowing them to carefully plan and then execute their course of action. Players have even more options than the first floor, but and also have the time to consider their possibilities.
The gameplay on the second floor presents more consolidated and discrete situations to players than the first floor, allowing them to carefully plan and then execute their course of action. Players have even more options than the first floor, but and also have the time to consider their possibilities.
Post-Mortem
What Went Well
Strong game pillars: The foundation and player experience goals for the game were established early on.
Productive lead meetings: The project leads were able to effectively communicate the project status and momentum in each discipline. I was able to communicate my ideas and direction of the game to the leads.
Responding to feedback: I quickly responded to playtester feedback and ensured that complaints and criticisms, especially by testers in our target audience, were appropriately addressed. It was important that Identity met the expectations of players who enjoy stealth, most notably ones who enjoy not using violence.
What Went Wrong
Lost work: Across the board, there was a significant amount lost work due to a variety of reasons from game design iteration to changing pipelines to simply not meeting standards of quality.
Tutorializing the player: We struggled to teach the player the game, partially due to the game's abstract nature. We hoped we could have a linear tutorial level that forced players to learn each mechanic in an actual level, but it wasn't obvious enough to players. Instead we added an interactive tutorial that was more explicit and prevented failure.
Impact of animations: The animation pipeline initially was very slow and ended up being a limiting factor for new features in the game. I did not communicate effectively with the animator early on and was out of the loop of how progress was moving. I would have made different decisions on both our ends if I was more involved.
What I Learned
Purpose-Driven stealth: Without a goal that is more substantial than "Go here!", players become disillusioned and get frustrated or bored rather quickly. This is especially true in stealth games with more abstract themes.
Explicit teaching is not bad: We were originally very nervous about condescending the player's intelligence with an explicit tutorial, but instead we found that that was exactly what players wanted in a game as abstract as ours.
How to say "No": There were several times in development when team members became very attached to ideas that were ultimately not healthy for the game. As a result, I had to firmly but kindly reject these ideas. It was not easy and not something I enjoyed, but not every idea is good and not every good idea can fit into any given game.